






Your external attack surface is constantly evolving, creating new risks from unknown assets, exposed services and misconfigurations. Below, we answer common questions about External Attack Surface Management and how DarkInvader helps security teams discover, monitor and prioritise external threats. If you need further clarity or a tailored demonstration, our team is here to help.
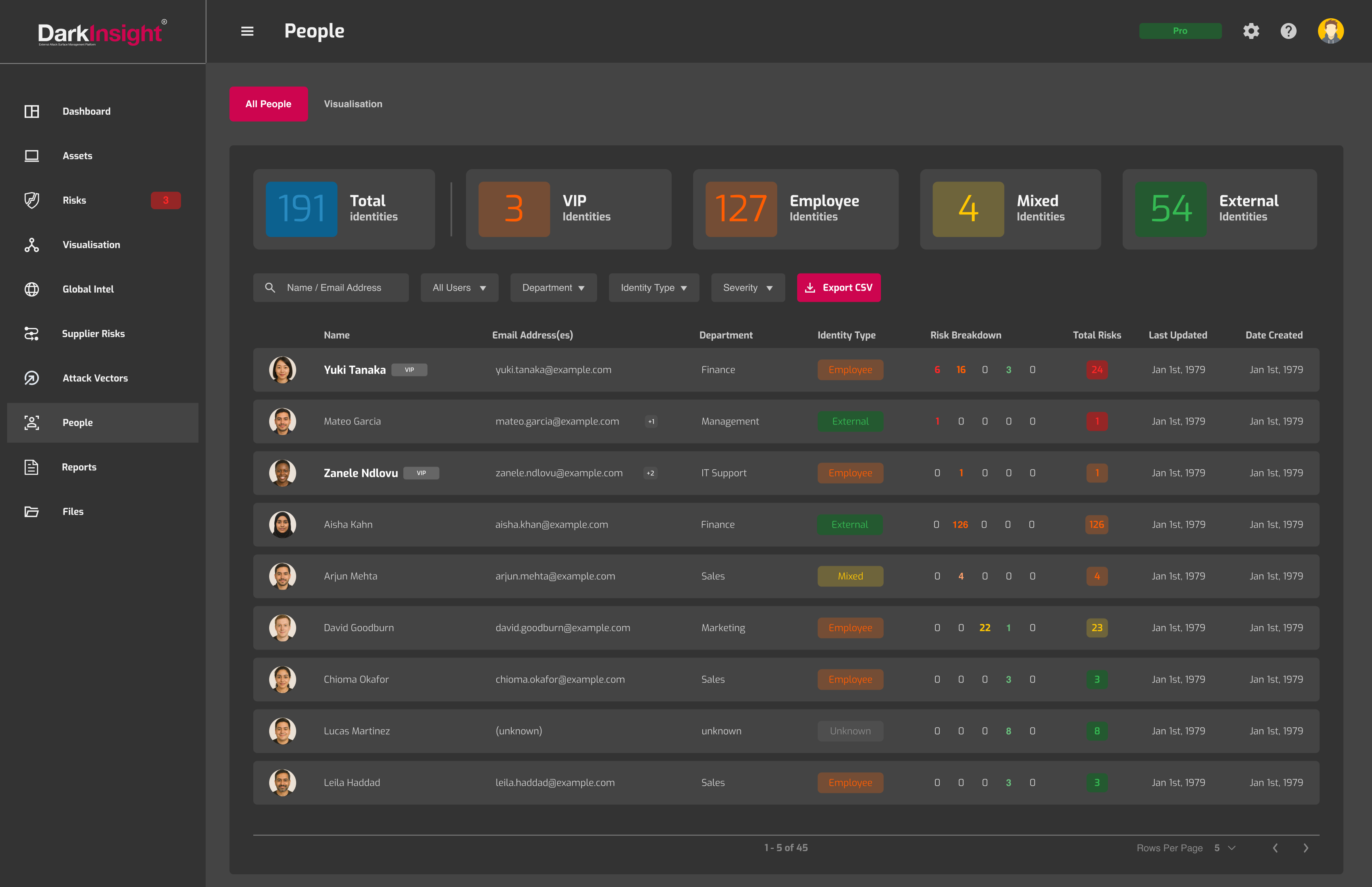
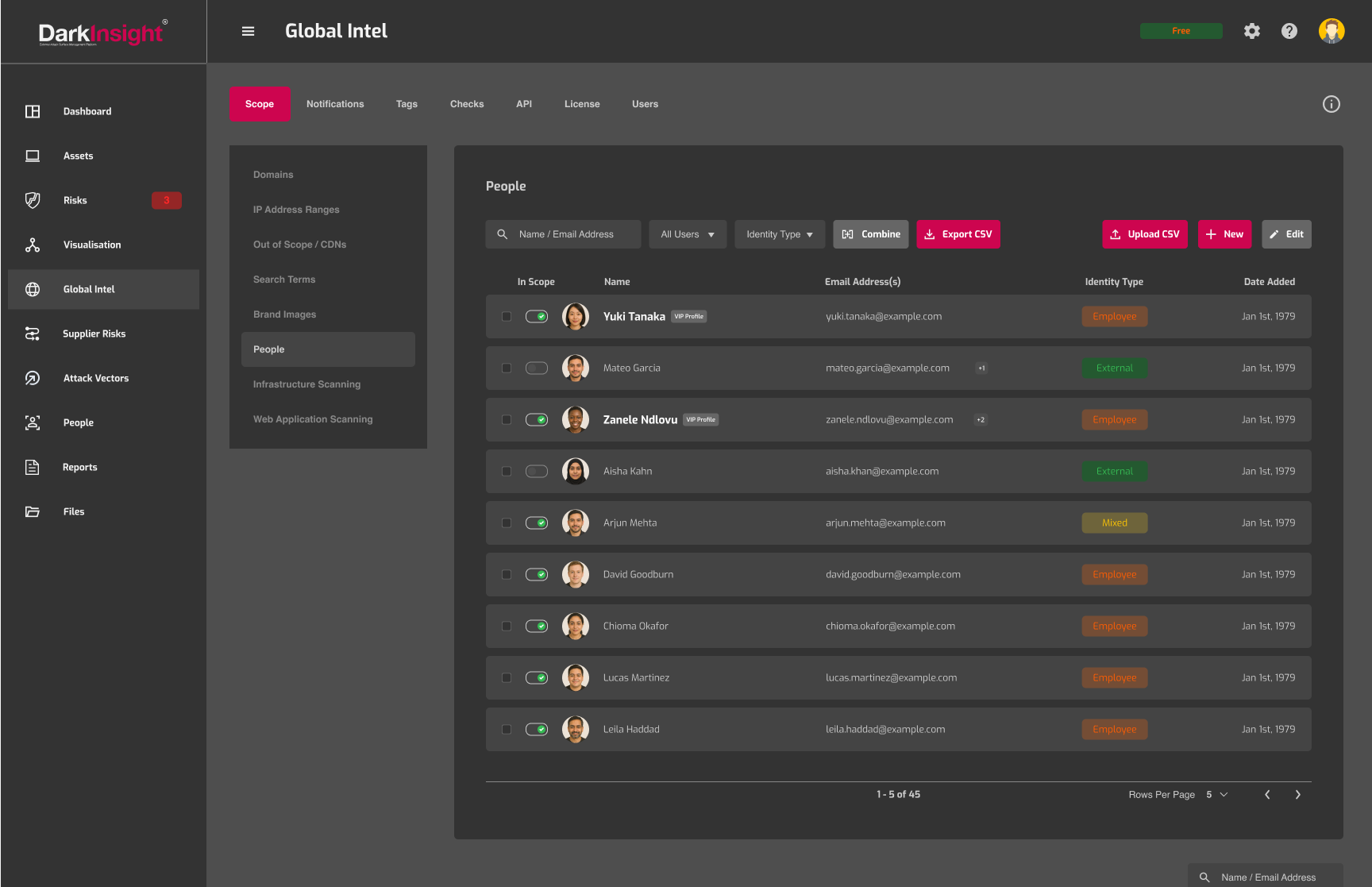
People monitoring focuses on identifying and assessing security risks linked to employees, executives and key personnel. Attackers frequently target individuals through phishing, credential theft and social engineering to gain access to corporate systems. Monitoring exposure associated with people helps organisations understand how the human layer contributes to overall attack surface risk.
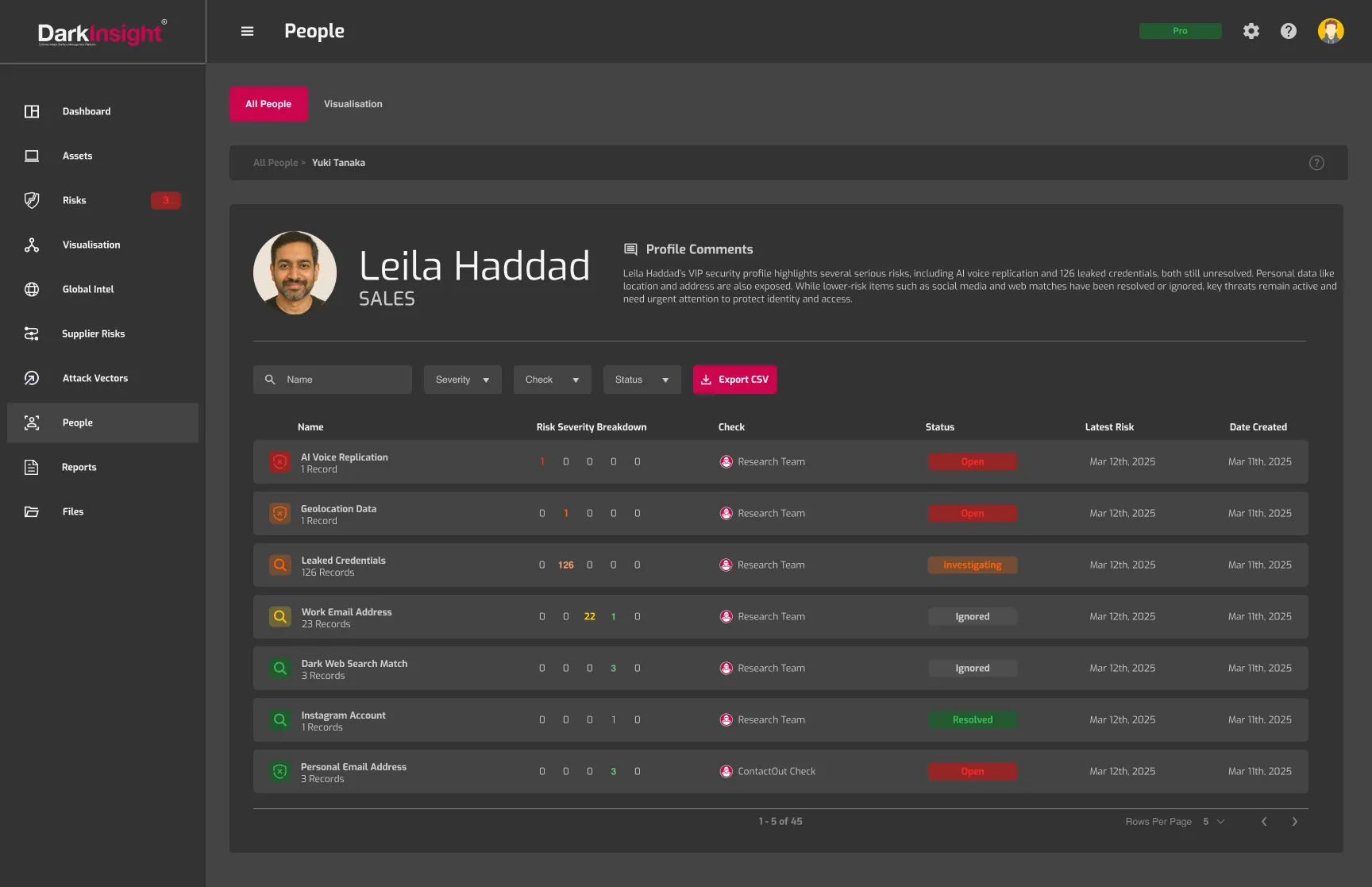
DarkInvader identifies exposed email addresses, leaked credentials, public profiles, impersonation attempts and references to key personnel in threat discussions. It also monitors for signs that individuals may be targeted in phishing campaigns or mentioned in underground forums. This visibility helps security teams assess potential entry points linked to human identity.
Social engineering attacks often begin with publicly available information about employees or executives. By identifying exposed data and monitoring for impersonation or targeting activity, organisations can take preventative measures such as enforcing stronger authentication controls, providing awareness training and limiting publicly accessible information.
Senior executives and privileged users are high-value targets due to their access levels and visibility. Compromised executive accounts can lead to significant financial, operational and reputational impact. Proactive monitoring helps detect exposure risks early and strengthen protective measures around critical individuals.
The human layer is a key component of the external attack surface. People monitoring complements technical asset discovery and vulnerability scanning by addressing identity-based risks. Integrated with other DarkInvader capabilities, it provides a more complete understanding of how attackers may target both infrastructure and individuals.
Unlock full visibility of your external attack surface with DarkInvader’s continuous, real-time monitoring. Create your free account to discover unknown assets, detect emerging risks and stay ahead of potential threats before attackers can exploit them.
Create My Free Account