As we stride confidently into the future, the landscape of cybersecurity is evolving at an unprecedented pace. With technology intertwined into every aspect of our lives, securing digital environments has become more crucial than ever. A pivotal force in this evolution is External Attack Surface Management (EASM), set to lead the charge in 2026 and beyond.
EASM is a proactive approach to managing and securing an organisation's cyber space, focusing specifically on external threats. Unlike traditional systems that often react to disclosures, EASM predicts and neutralises potential vulnerabilities before they manifest into critical issues. It's akin to having an advanced intel system, keeping an eagle-eyed watch over an organisation's most exposed areas.
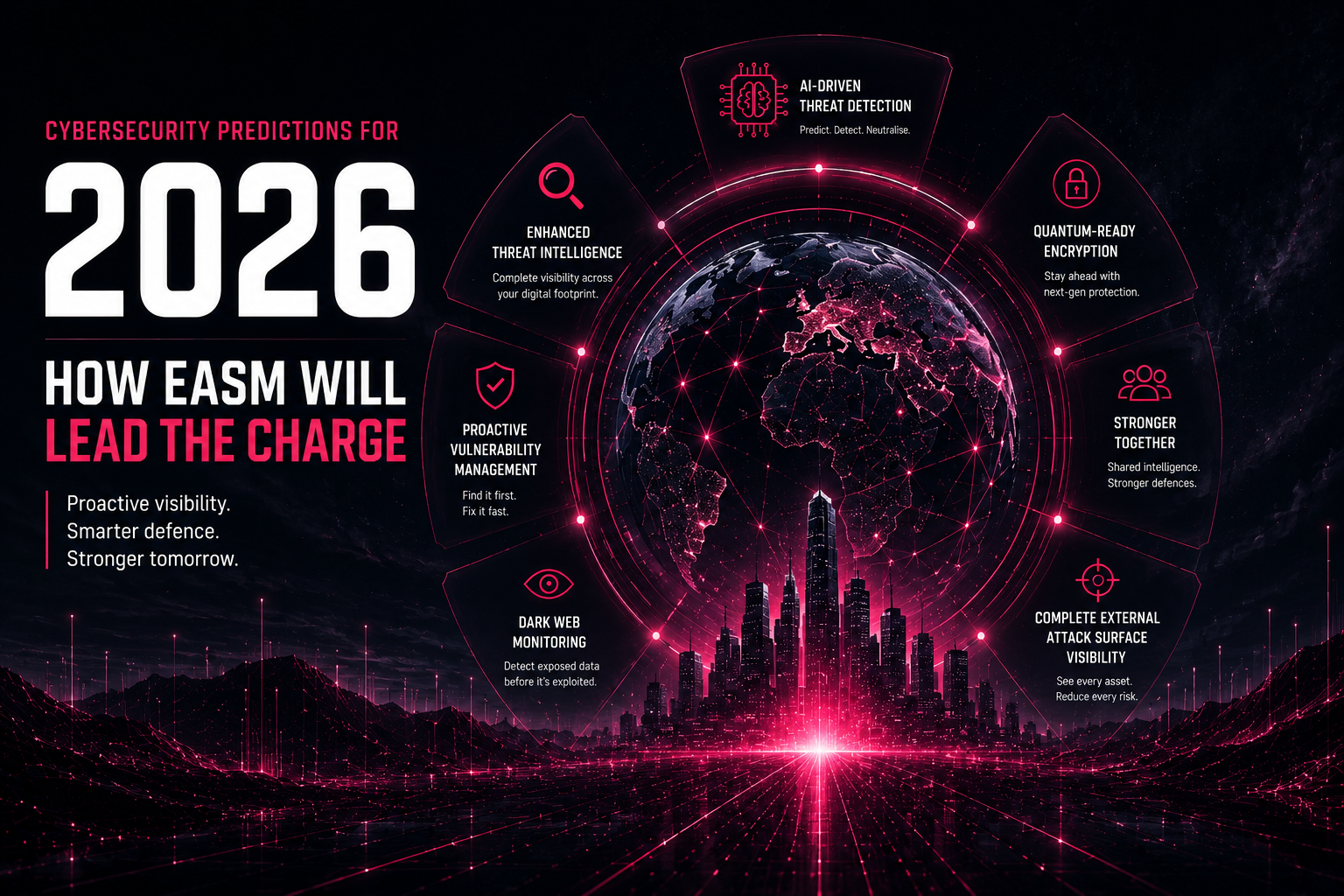
Artificial Intelligence (AI) and Machine Learning (ML) are at the forefront of cybersecurity advancements. By 2026, AI-driven security systems will not only predict threats but autonomously counteract them. This capability is essential in deciphering patterns from massive volumes of data, enabling sophisticated threat responses in real-time.
Moreover, the integration of AI with EASM provides unmatched capabilities to detect anomalies within an organisation's digital footprint. This synergy significantly enhances threat detection efficiency, making it a formidable shield against cyberattacks.
Quantum computing is another frontier that will redefine cybersecurity. With its incomprehensible processing power, it promises to crack even the most robust encryption protocols if left unchecked. However, it also offers new encryption methodologies that are virtually unbreakable.
By employing such advanced technologies within EASM, organisations can remain one step ahead, relying on quantum-resistant algorithms for safeguarding data integrity.
EASM heightens threat intelligence by encompassing a comprehensive overview of all digital assets, identifying even the most obscure vulnerabilities. This includes monitoring for leaked credentials, brand misrepresentation, and shadow IT that can unwittingly expose companies to risk.
A proactive stance toward vulnerability management is what sets EASM apart from conventional methods. Through continuous scanning and monitoring, it ensures all potential entry points are fortified against intrusions. It’s like having a digital sentinel safeguarding perimeter integrity against cyber marauders.
Adding another layer of protection, Dark Web monitoring within EASM frameworks alerts organisations to potential breaches being discussed or sold on illicit platforms. This holistic approach offers peace of mind, knowing actions can be taken long before an exploit becomes public.
Beyond individual innovations, the collaborative aspect of cybersecurity cannot be overstated. Sharing threat intelligence across sectors fortifies a collective defence against cyber adversaries. As threats grow in complexity, collaboration between businesses, governments, and cybersecurity firms like DarkInvader will prove invaluable.
With emerging technologies like blockchain becoming more mainstream, integrating them with EASM could further enhance data security and transparency. IoT devices, proliferating in both personal and industrial spaces, highlight the necessity for evolving security strategies. As these devices interact with networks worldwide, EASM will be instrumental in ensuring every node remains protected against unauthorised access and data breaches.
As we forecast into 2026, EASM is positioned not merely as a component of cybersecurity but as a strategic partner in organisational resilience. The continuous evolution of cyber threats demands robust, comprehensive solutions, and EASM provides exactly that—an intricate, proactive approach essential for modern cyber defence strategies.
Unlock full visibility of your external attack surface with DarkInvader’s continuous, real-time monitoring. Create your free account to discover unknown assets, detect emerging risks and stay ahead of potential threats before attackers can exploit them.
Create My Free Account