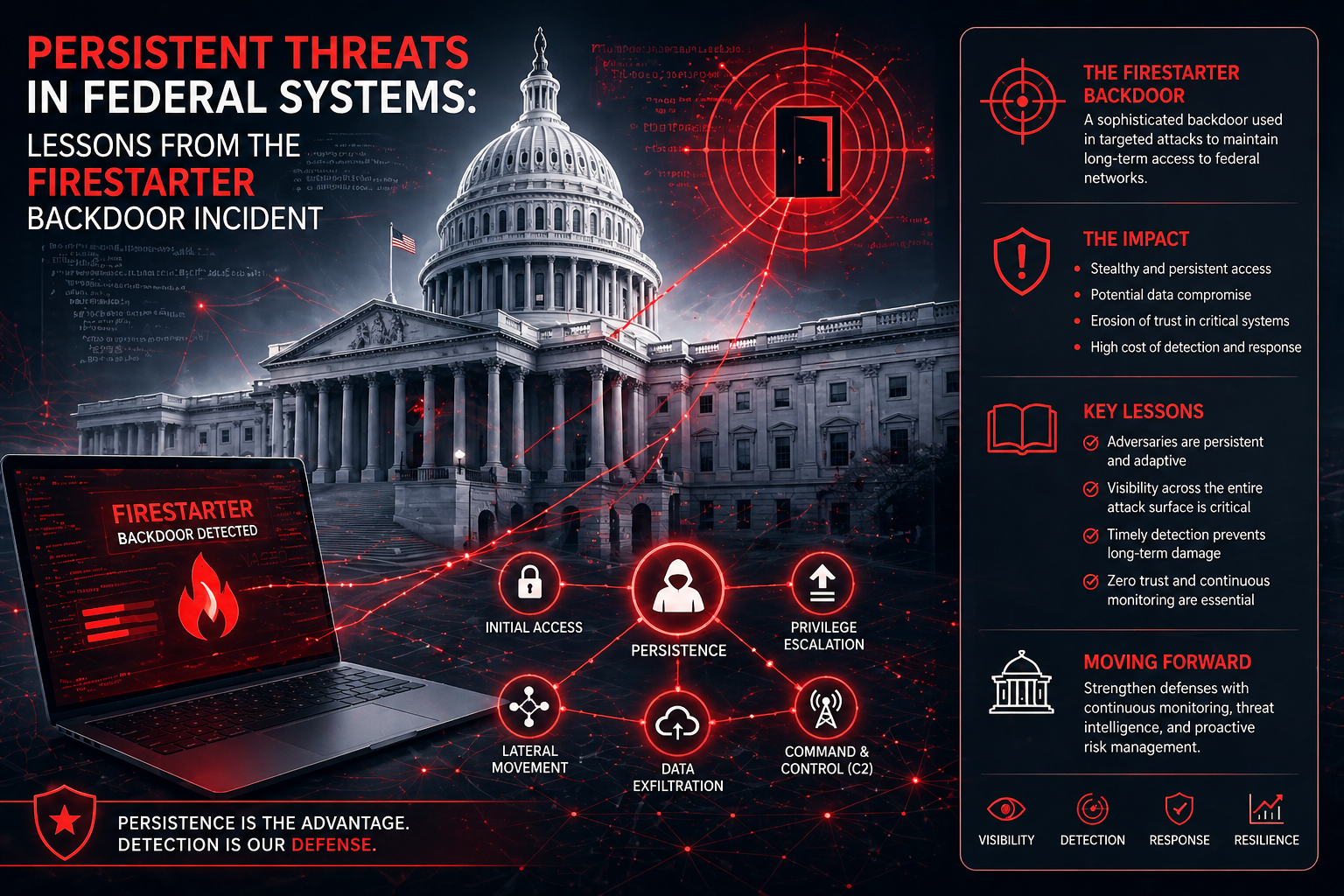
The cyber world is often likened to an ever-evolving battlefield, where sophisticated, persistent threats lurk in the digital shadows. This analogy became particularly apt with the emergence of the FIRESTARTER backdoor incident. By infiltrating federal systems, this event underlined not only the vulnerability of governmental cyber defences but also the talent and tenacity of cyber adversaries. This blog post delves into the intricacies of the FIRESTARTER backdoor, examines the lessons learned, and suggests routes to bolster resilience against such insidious threats.
FIRESTARTER is a term now etched into the annals of cyber threats. This particular backdoor was designed with precision, allowing attackers clandestine access into federal systems. Unlike typical malware, a backdoor circumvents traditional security protocols, using innovative methods to stealthily enter and exploit systems.
A backdoor like FIRESTARTER usually consists of executable code designed to bypass authentication. It establishes a connection between the compromised system and the attacker, often enabling data exfiltration, surveillance, or even system control. The challenge for cybersecurity professionals is in the stealthy deployment of these backdoors, which can remain undetected for extended periods.
The incursion into federal systems through FIRESTARTER had significant consequences. Not only was sensitive data compromised, but it also set off alarms regarding national security. Such breaches highlight vulnerabilities in the architecture of federal systems, magnifying the need for stringent cybersecurity protocols.
While the initial breach caught many by surprise, the subsequent analysis of the incident provided crucial insights into preventing future occurrences.
The FIRESTARTER incident emphasised the benefits of comprehensive vulnerability scanning. Regular scans can identify and mitigate vulnerabilities before they are exploited. Federal systems can no longer rely solely on perimeter defences; they must adopt a zero-trust architecture, scrutinising all activities within and outside the network.
In the realm of cybersecurity, knowledge is power. The deployment of a robust global threat intelligence framework is vital. Real-time analysis of threat intelligence can provide early warnings about new backdoor methods, assisting in pre-emptive defence strategies.
Establishing thorough monitoring protocols, as outlined by tools like OSINT monitoring and dark web surveillance, ensures timely detection of anomalies. This proactive approach can neutralise threats before they gain a foothold, promoting a preventive rather than a reactive cybersecurity posture.
In the wake of the FIRESTARTER incident, how do federal systems evolve to prevent such breaches?
Awareness and training are foundational to a resilient cybersecurity strategy. Agencies must invest in employee training to recognize spear phishing attempts and other tactics used to introduce backdoors like FIRESTARTER.
Federal systems must harness the expertise of dedicated cybersecurity teams. Collaborating with agencies like DarkInvader's research team can enhance understanding and readiness against evolving threats. Real-world solutions are often found at the intersection of academic research and industry practice.
Government bodies must implement policies that keep pace with technological advancements. Cybersecurity policies should mandate regular audits and establish clear protocols for responding to breaches, thereby reinforcing their defences against threats like FIRESTARTER.
The FIRESTARTER backdoor incident has served as a stark reminder of the need for vigilance, robust defenses, and a proactive approach to cybersecurity. As federal systems continue to digitize, the resilience of these systems against persistent threats is non-negotiable. By adopting comprehensive monitoring solutions, stringent protocols, and industry collaboration, the path towards a more secure digital future is attainable.
A backdoor is a hidden method for bypassing normal authentication or securing remote access to a computer. Unlike front-door cyber attacks, backdoors allow hidden intrusions without raising alarms, making them particularly dangerous.
The FIRESTARTER incident compromised sensitive data within federal systems and highlighted the need for improved cybersecurity measures. It illustrated gaps within existing defenses and prompted a comprehensive review of security protocols.
Protecting against backdoor threats requires a combination of vulnerability scanning, threat intelligence, employee cybersecurity education, and collaboration with industry experts to stay ahead of evolving threats.
Preventive measures include implementing a zero-trust architecture, regular system audits, continuous monitoring, and establishing stringent security policies. Investing in training and advanced cybersecurity solutions also fortifies defences against potential threats.
Unlock full visibility of your external attack surface with DarkInvader’s continuous, real-time monitoring. Create your free account to discover unknown assets, detect emerging risks and stay ahead of potential threats before attackers can exploit them.
Create My Free Account